Transform Your Supply Chain Planning and Marketing Strategies with Google Cloud and SAP Integration
Transform Your Supply Chain Planning and Marketing Strategies with Google Cloud and SAP Integration
June 28, 2021 | Suraj Bawane
Blog / Google Workspace Investigation Tools
The Security Center Detection Tool is not just any other tool that searches for and removes email logs. It is not a reporting tool that displays logs and helps create fancy reports.
It is not just a device that a user can see for a device and erase it. Furthermore, it is not just a tool that checks a user’s failed login checks and suspends the user.
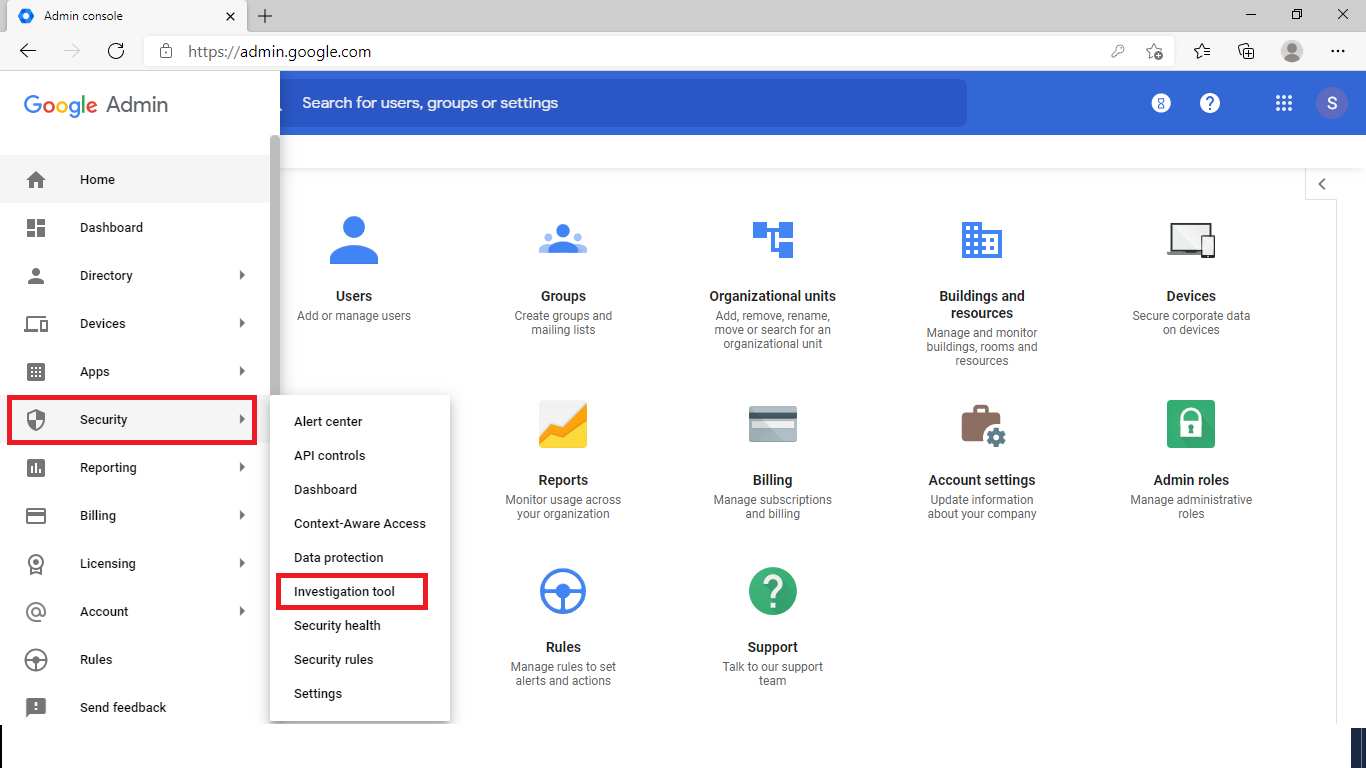
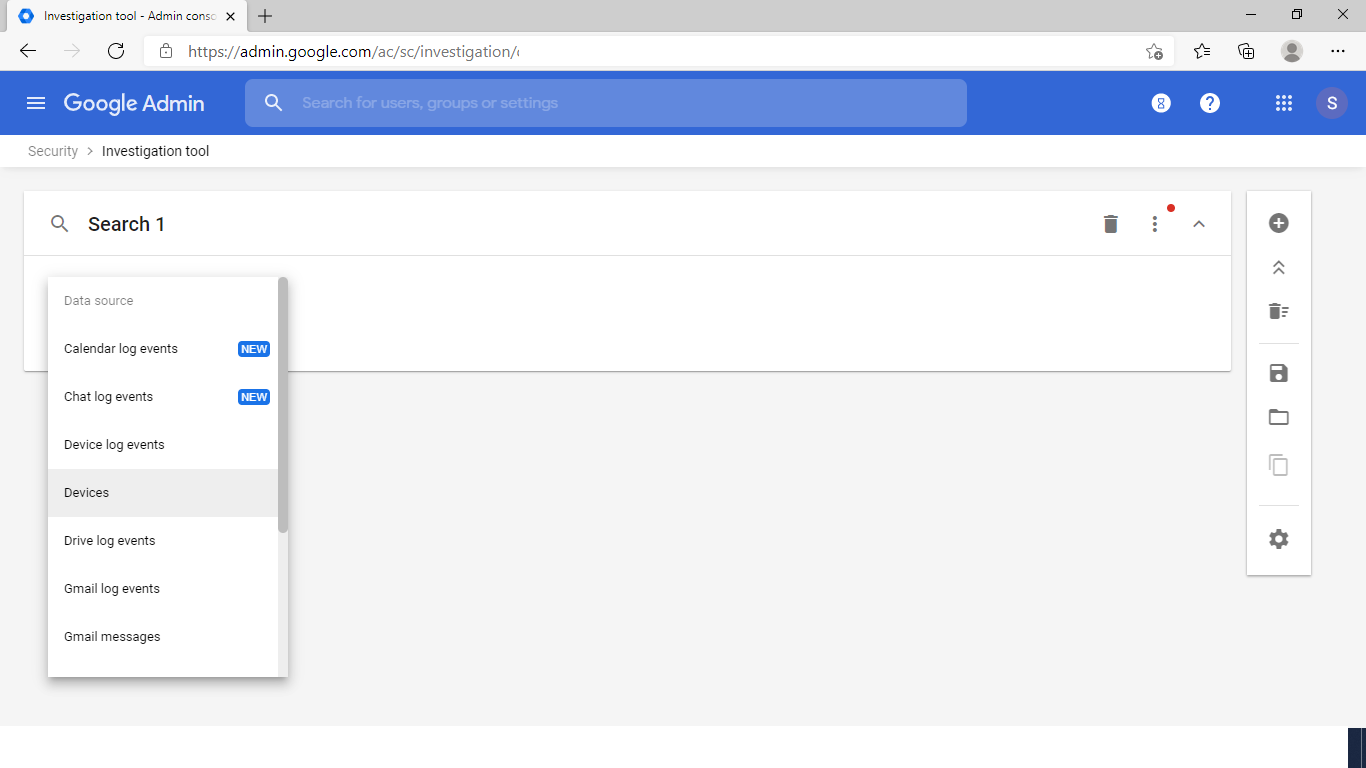
It is a centralized tool used to manage any alerts and logs related to all users, devices, email and drive events.
Unlike other cloud solutions within the Security and Compliance Center for DLP, data governance, record management, etc. there is no need to have separate tabs.
Ultimately, it boils down to an investigative device in all Google Workspace – which will be the security center.
Whether it is looking for email sent by a specific user or checking access permissions on a particular user’s drive document, or remote wipe of a user device, All this can be done with a central device.
This can be an ideal place to start looking for an IP address from where an email is originating or clicked on a link to a user’s email to find out as granular Can.
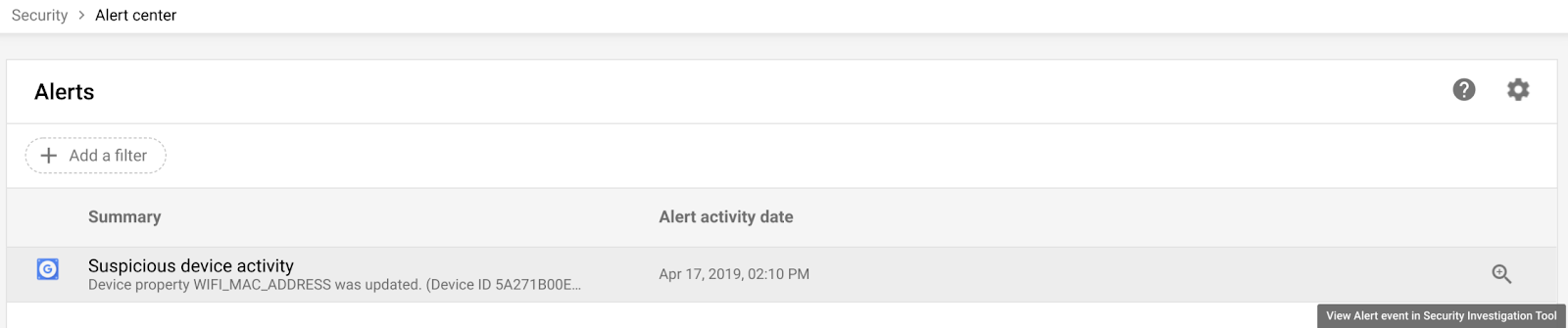
It is also strongly integrated with the Security Alert Center, The way that a particular alert can be triggered can be checked directly from there.
This usually becomes a case where an administrator can actually suspend a user or delete a document that is shared externally, When they detect or suspect data leaks. But this is not the case when customers are powered by Google Workspace.
When searching for sheets or docs shared by users, it is possible to retrieve not only the document list, but also revoke or edit a particular user’s access permissions for a particular document.
It is also possible to implement disabling of download, print and copy for the document directly by the administrator.
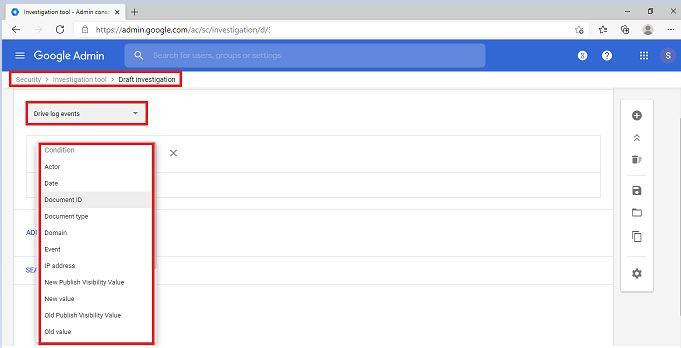
With a single search query, it is possible to retrieve all documents that can be shared externally.
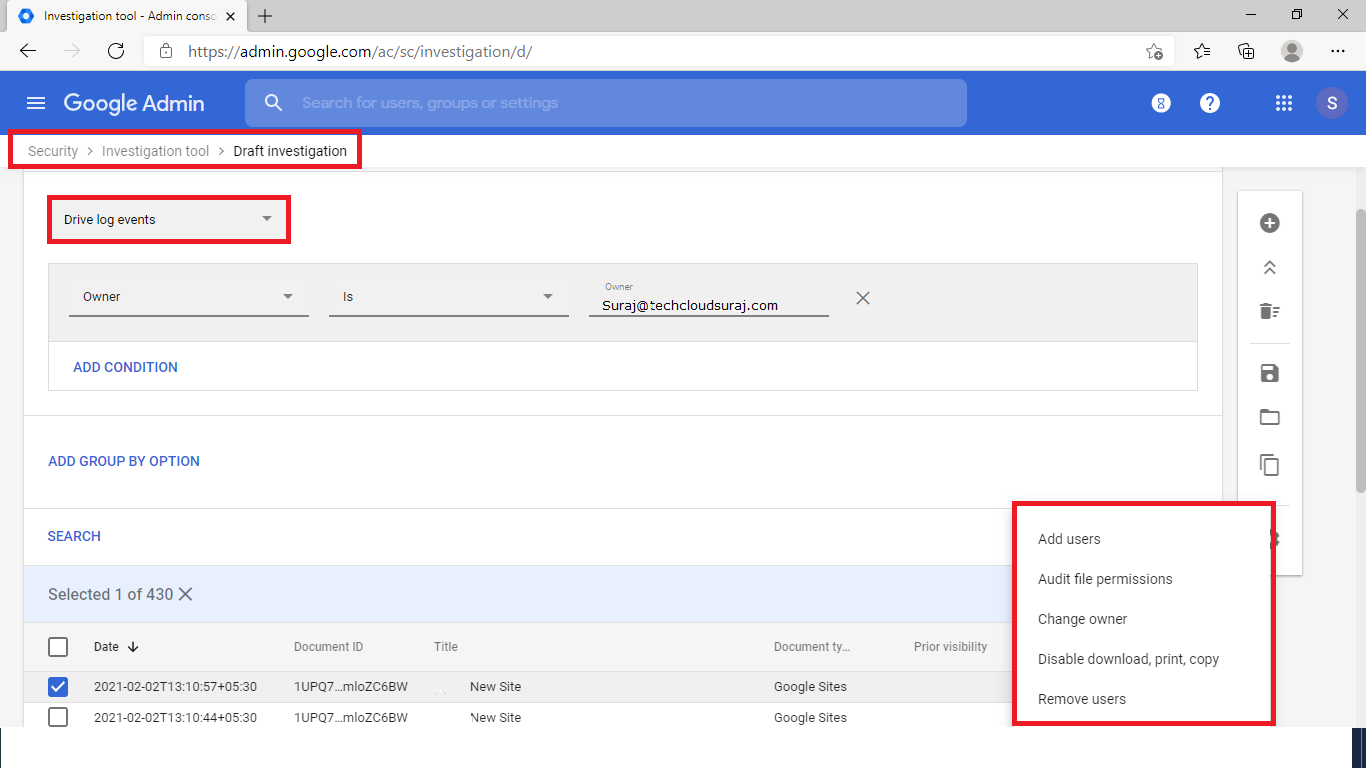
Another very common scenario in drive-related probes is when file visibility changes within drive or shared drive permissions. The options for investigation are simply numerous.
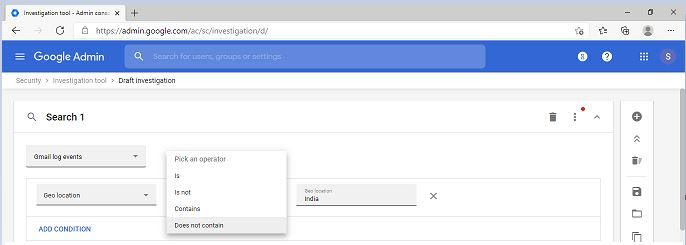
Whether it is searching for an original IP address or searching for emails based on the attached hash, the same can be done from the Granular Lookup Check Center. Emails with a particular content can be searched or deleted in all mailboxes of the organization at once, or any item from a single user mailbox.
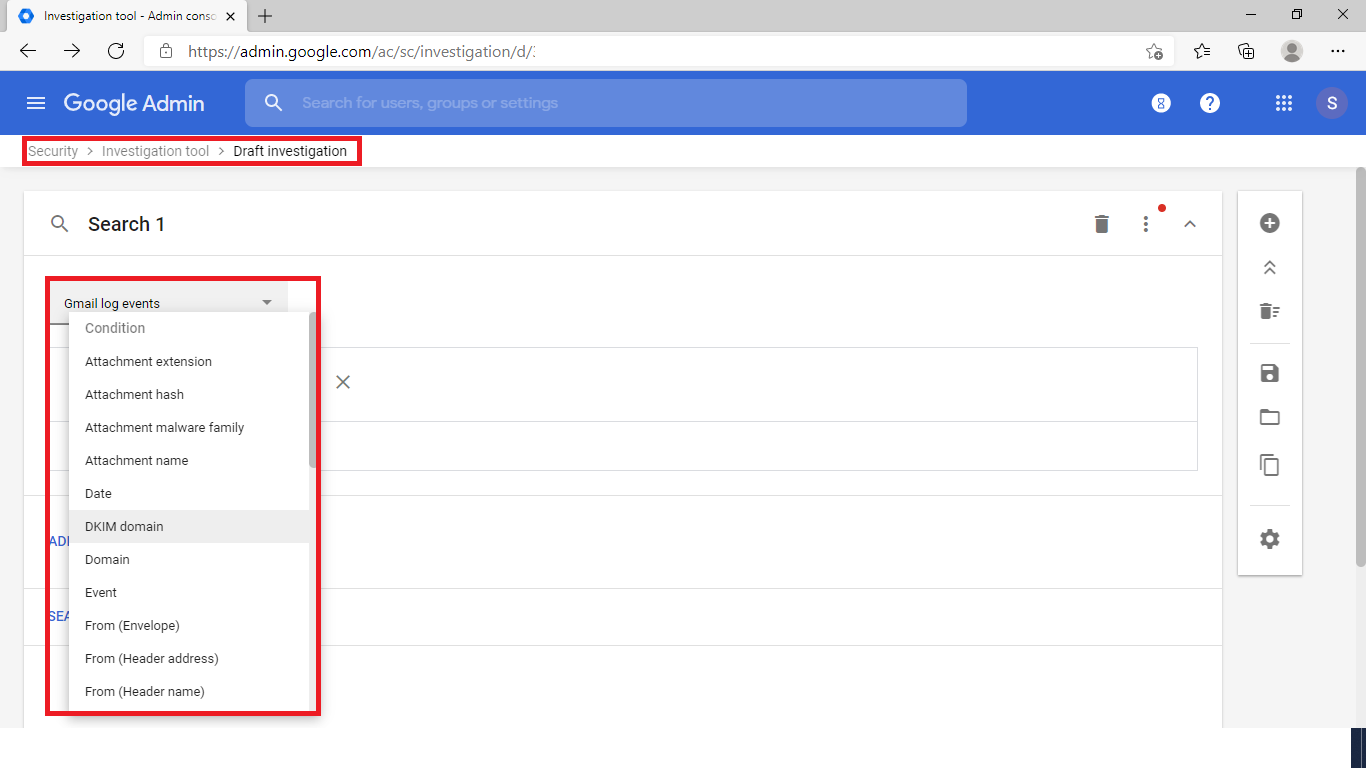
Whether it is a link click or an attachment saved to a link or even a drive within an attachment click, events can still be excluded.
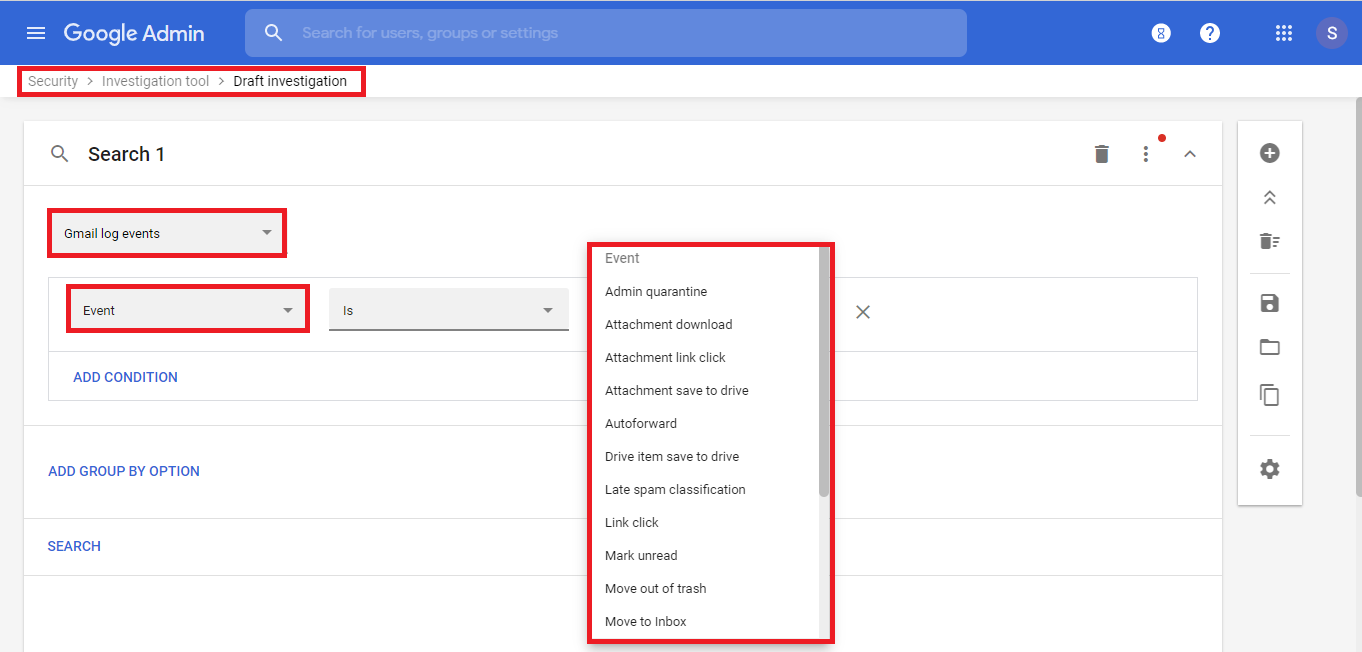
Search is also done from the same location based on spam classification.
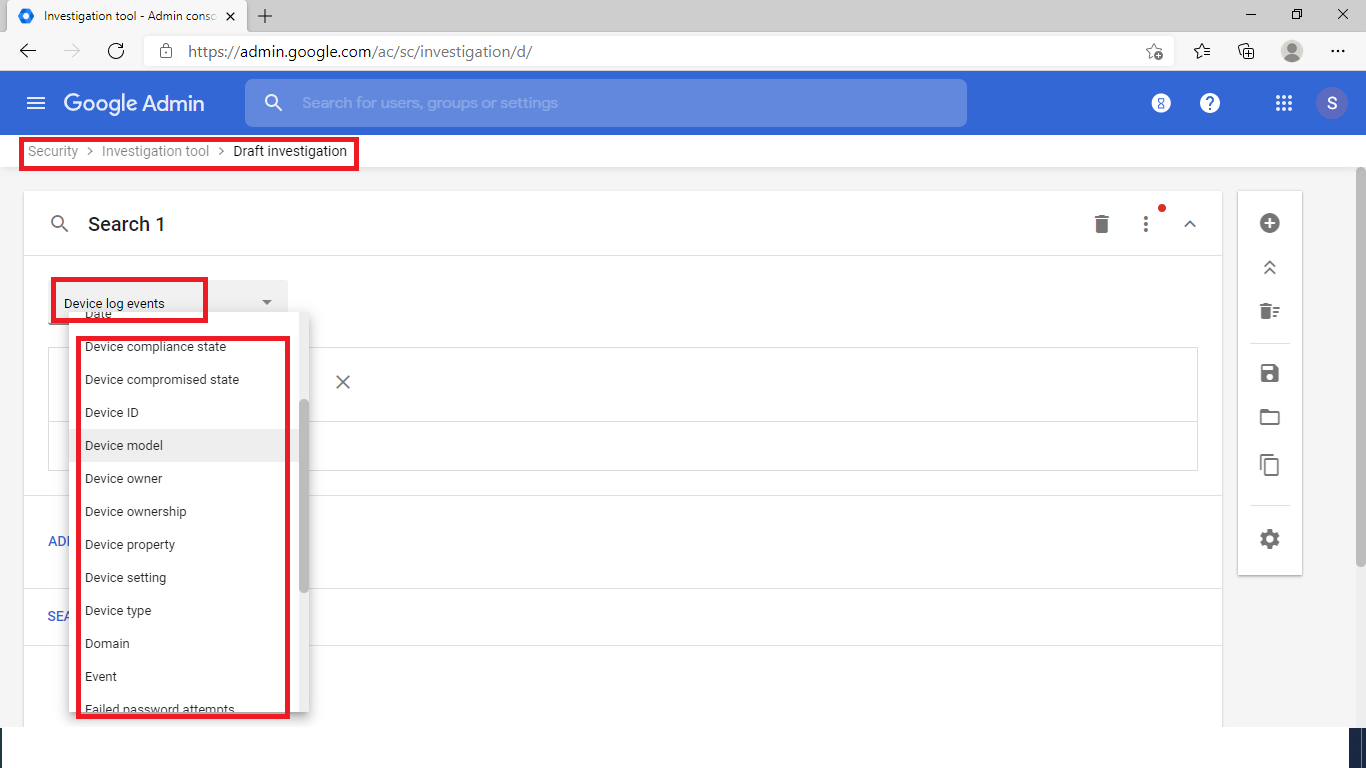
Whether it is a probe based on device model, owner, sync state, password, or other device specific details, or whether it is device log related events such as failed password events or compromised states or many more, this re-check center There are about 40 related equipment first level options available for testing. Device actions can be taken based on several details populated for the event such as remote wipe off or quarantining the device.
Depending on the user’s first name, password change status, 2FA status and many other options, events can also be searched and actions taken in the user’s account accordingly.
Google is bringing more and more enhancements in this area. There is a latest feature edition (beta release) that will enable entry with 2 additional capabilities within the Google Workplace Safety Center testing tool Save and share probes in the security check tool Create rules inside the Safety Center to perform automated actions